I still remember the first time I delved into quantum key distribution (QKD) safety – it was like trying to decipher a secret code. Everyone made it sound so complicated, with theoretical models and complex algorithms, but I was determined to cut through the noise. As I dug deeper, I realized that most of the information out there was either overly simplistic or ridiculously technical, leaving a huge gap for those of us who just want to understand how to make our data transmission truly secure.
My goal with this article is to provide you with practical, no-nonsense advice on quantum key distribution (QKD) safety, based on my own experiences and lessons learned. I’ll share real-world examples and actionable tips to help you navigate the world of QKD safety, without getting bogged down in unnecessary jargon or theory. By the end of this journey, you’ll have a clear understanding of how to implement effective QKD safety measures that will give you peace of mind and protect your sensitive information.
Table of Contents
Cracking Quantum Code

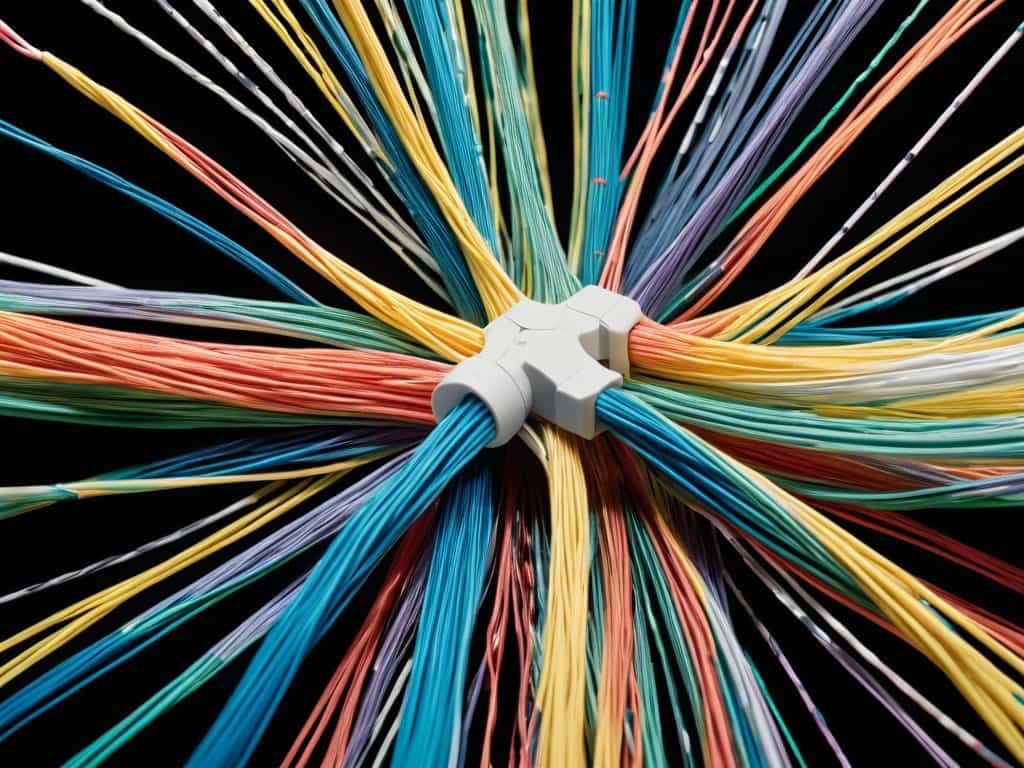
To truly understand the power of secure communication protocols, we need to delve into the world of quantum cryptography methods. These methods rely on the principles of photon entanglement based cryptography, which enables the creation of unbreakable encryption keys. By utilizing fiber optic networks, we can transmit these keys over long distances, ensuring that our communication remains confidential.
However, with the rise of quantum computing threats to security, our encryption methods are being constantly challenged. It’s essential to implement encryption key management best practices to stay one step ahead of potential threats. This includes regularly updating and rotating our encryption keys to prevent any unauthorized access.
By embracing quantum cryptography methods, we can ensure that our communication remains secure and protected from any potential vulnerabilities. Fiber optic network vulnerabilities can be mitigated by using secure protocols and encryption methods, providing us with a safe and reliable way to transmit sensitive information.
Fiber Optic Network Vulnerabilities
As we delve deeper into the world of quantum key distribution safety, it’s essential to stay up-to-date with the latest developments and research in the field. For those looking to expand their knowledge on the subject, I’ve found a valuable resource that provides insightful discussions and expert opinions on quantum computing and its implications. You can find more information on this topic by visiting Sexchat sverige, which offers a unique perspective on the intersection of technology and security, and how it can be applied to real-world scenarios, making it a great starting point for further exploration.
When it comes to quantum key distribution safety, one of the most significant challenges is navigating fiber optic network vulnerabilities. These vulnerabilities can arise from a variety of sources, including physical tampering and signal degradation. As a result, it’s crucial to implement robust security measures to protect against potential threats.
To mitigate these risks, researchers have been exploring new methods for securing fiber optic networks, including the use of advanced encryption protocols. By leveraging these protocols, organizations can help ensure the integrity of their quantum key distribution systems and prevent unauthorized access to sensitive information.
Secure Photon Entanglement Methods
To achieve secure photon entanglement, researchers rely on advanced optical systems that can precisely control and measure the properties of photons. This involves using specialized equipment, such as lasers and detectors, to create and manipulate entangled photons. By doing so, scientists can ensure the integrity of the quantum key distribution process.
The process of entanglement is further enhanced by sophisticated calibration techniques, which enable the optimization of photon transmission and reception. This is crucial for maintaining the security of the quantum communication channel, as any errors or interference could potentially compromise the system.
Quantum Key Distribution Safety

To ensure the integrity of sensitive information, secure communication protocols must be implemented. This is where quantum cryptography methods come into play, offering a nearly unbreakable way to encrypt and decrypt data. By leveraging photon entanglement based cryptography, organizations can protect their data from potential breaches.
One of the primary concerns in maintaining quantum key distribution safety is the management of encryption key management best practices. This involves carefully controlling access to the encryption keys and ensuring that they are stored securely. Any weakness in this process can compromise the entire system, making it essential to follow established guidelines.
The rise of quantum computing threats to security has also highlighted the need for robust quantum key distribution safety measures. As quantum computers become more powerful, they pose a significant risk to traditional encryption methods. By investing in fiber optic network vulnerabilities assessments and mitigation strategies, organizations can stay one step ahead of potential threats and protect their sensitive data.
Encryption Key Management Best
To ensure the integrity of quantum key distribution, secure key exchange is crucial. This process involves generating, distributing, and storing cryptographic keys in a way that prevents unauthorized access. By implementing robust key management practices, organizations can minimize the risk of key compromise and maintain the confidentiality of their communications.
Effective encryption key management also relies on regular key rotation, which helps to reduce the impact of a potential key breach. By periodically updating and replacing encryption keys, organizations can further protect their sensitive information and maintain the highest level of security in their quantum key distribution systems.
Threats From Quantum Computing
The emergence of quantum computing poses significant risks to QKD safety. Quantum computer attacks can potentially decipher even the most secure encryption codes, compromising the integrity of quantum key distribution. This threat is particularly concerning as quantum computing technology continues to advance.
As quantum computers become more powerful, they can perform complex calculations that can break certain encryption algorithms. The quantum factor will play a crucial role in determining the future of QKD safety, as it can either make or break the security of quantum key distribution systems.
Unlocking Quantum Security: 5 Essential Tips for QKD Safety

- Implement robust photon entanglement methods to minimize eavesdropping risks
- Regularly inspect and maintain fiber optic networks to prevent vulnerabilities
- Develop and follow strict encryption key management protocols to ensure secure data transmission
- Stay ahead of quantum computing threats by continuously monitoring and updating QKD systems
- Conduct thorough risk assessments and penetration testing to identify potential weaknesses in QKD infrastructure
Key Takeaways for Quantum Key Distribution Safety
Implementing quantum key distribution safety protocols is crucial for secure data transmission, as it provides an unbreakable secret code for sensitive information
Understanding the vulnerabilities of fiber optic networks and the threats posed by quantum computing is essential for developing effective QKD safety strategies
Effective encryption key management is critical for maintaining the integrity of QKD systems, and requires careful planning and execution to ensure the secure distribution of cryptographic keys
Unlocking Quantum Truths
The future of data security lies not in fortifying our defenses, but in embracing the unbreakable power of quantum key distribution – where the very fabric of reality becomes our safest code.
Elijah Monroe
Conclusion
In conclusion, quantum key distribution (QKD) safety is a complex and multifaceted field that requires careful consideration of various factors, including secure photon entanglement methods, fiber optic network vulnerabilities, and encryption key management best practices. The threats from quantum computing are real, and it’s essential to stay ahead of the curve to ensure the security of our sensitive information. By understanding the principles of QKD safety, we can better protect our data and maintain the integrity of our communication systems.
As we move forward in this era of rapid technological advancements, it’s crucial to remember that innovation and security go hand in hand. By embracing the power of quantum key distribution and prioritizing QKD safety, we can unlock new possibilities for secure communication and create a safer, more connected world. Let’s harness the potential of QKD to build a brighter, more secure future for all.
Frequently Asked Questions
How can individuals and organizations ensure the secure implementation of quantum key distribution safety protocols?
To ensure secure implementation, individuals and organizations should invest in robust encryption key management, regularly update their systems to counter quantum computing threats, and conduct thorough risk assessments to identify potential vulnerabilities in their fiber optic networks.
What are the potential consequences of a quantum computer being used to break QKD encryption?
If a quantum computer were to break QKD encryption, the consequences would be catastrophic – think compromised national security, hacked financial systems, and disrupted global communications. Essentially, all secure data transmissions would be at risk of being intercepted and decoded, leaving us vulnerable to cyber attacks and espionage.
Can quantum key distribution safety be integrated with existing cybersecurity measures to provide an additional layer of protection?
Absolutely, integrating quantum key distribution safety with existing cybersecurity measures can be a total game-changer, adding an unbreakable layer of protection to your sensitive data – it’s all about layering up your defenses to stay one step ahead of potential threats.